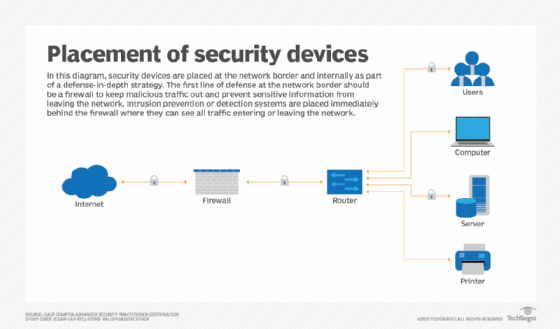
Network Security Perimeter: How to choose the correct firewall and IPS for your environment? - SANS Internet Storm Center
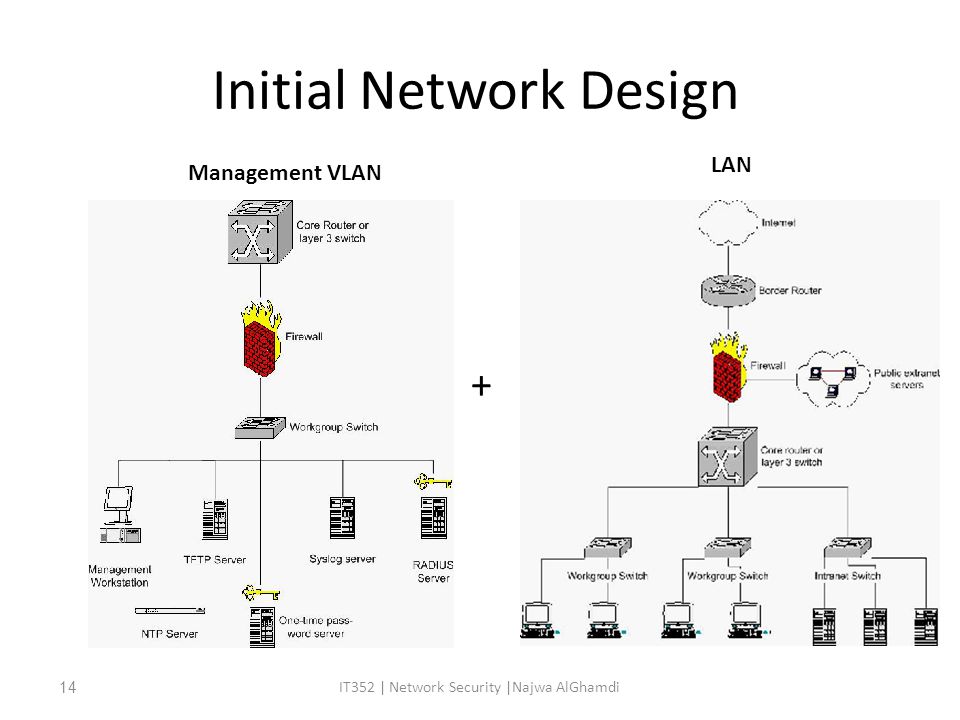
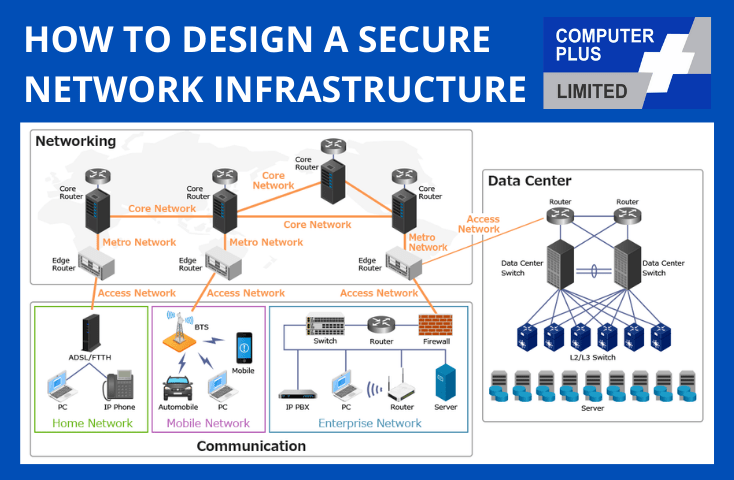
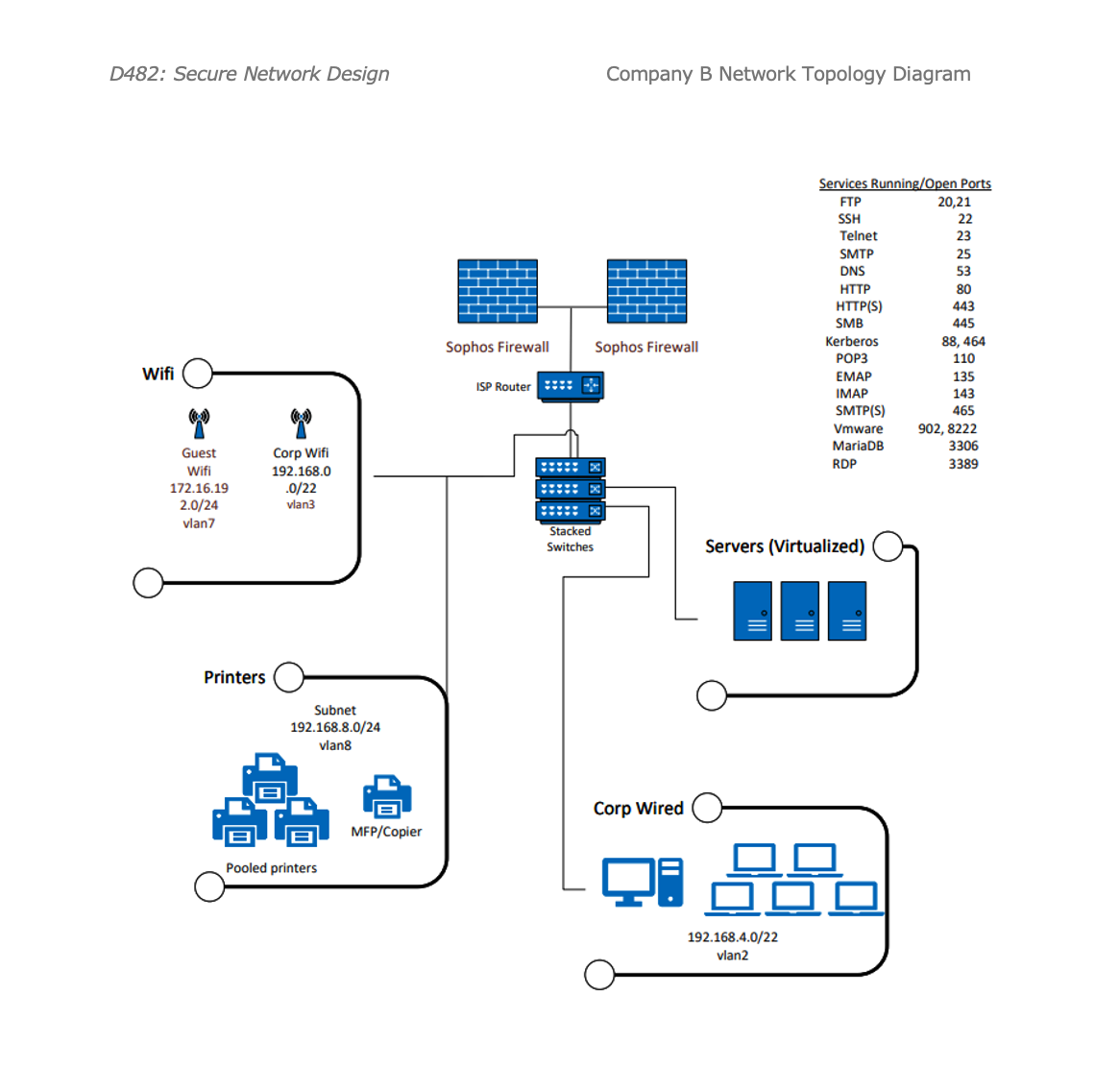
Secure Network Design: Designing a Secure Local Area Network IT352 | Network Security |Najwa AlGhamdi1 Case Study - ppt download

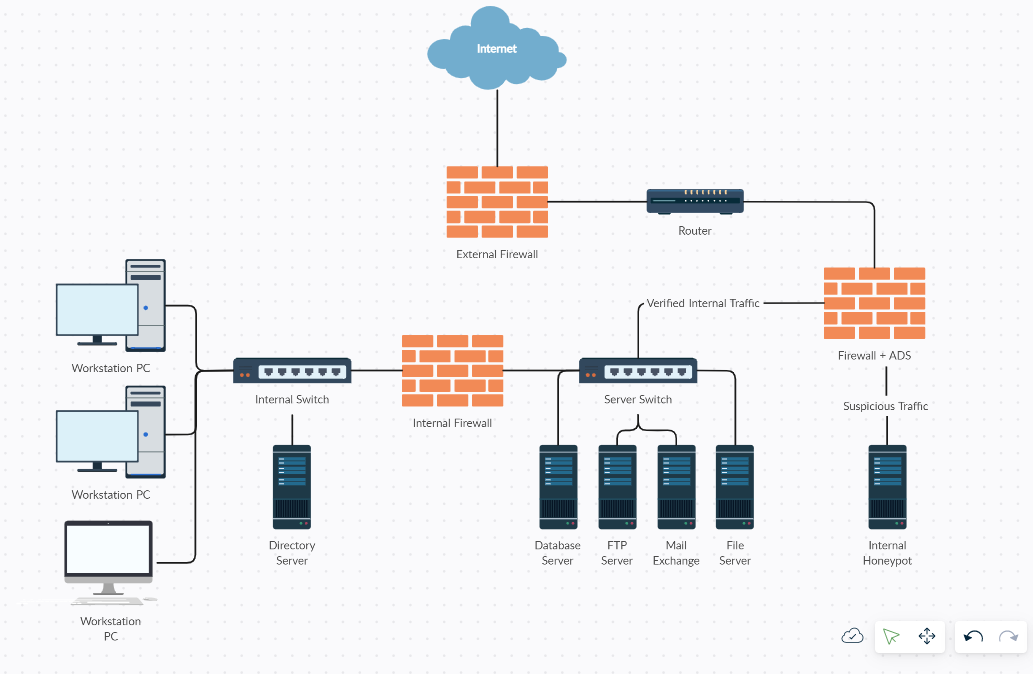
Figure 1 from Design and Implementation of a Network Security Model for Cooperative Network | Semantic Scholar

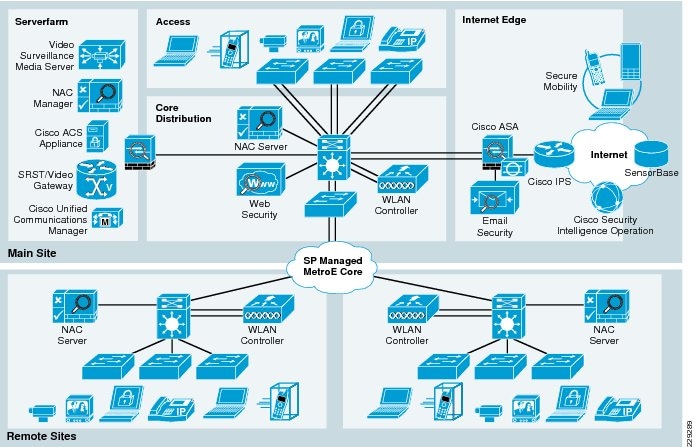
Design of the secure network model by the paper "Threat Minimization by... | Download Scientific Diagram

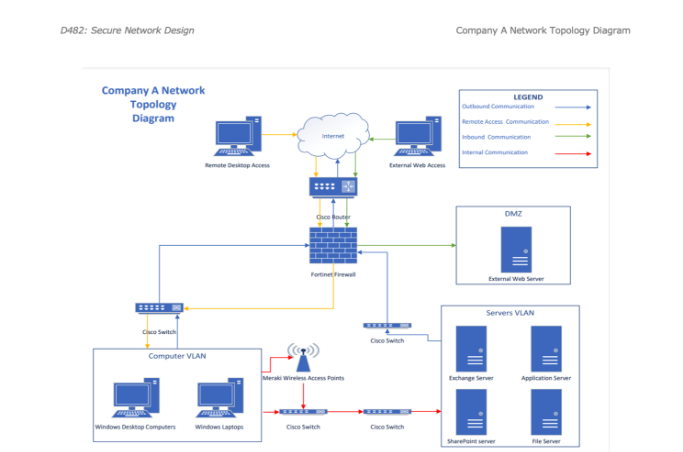
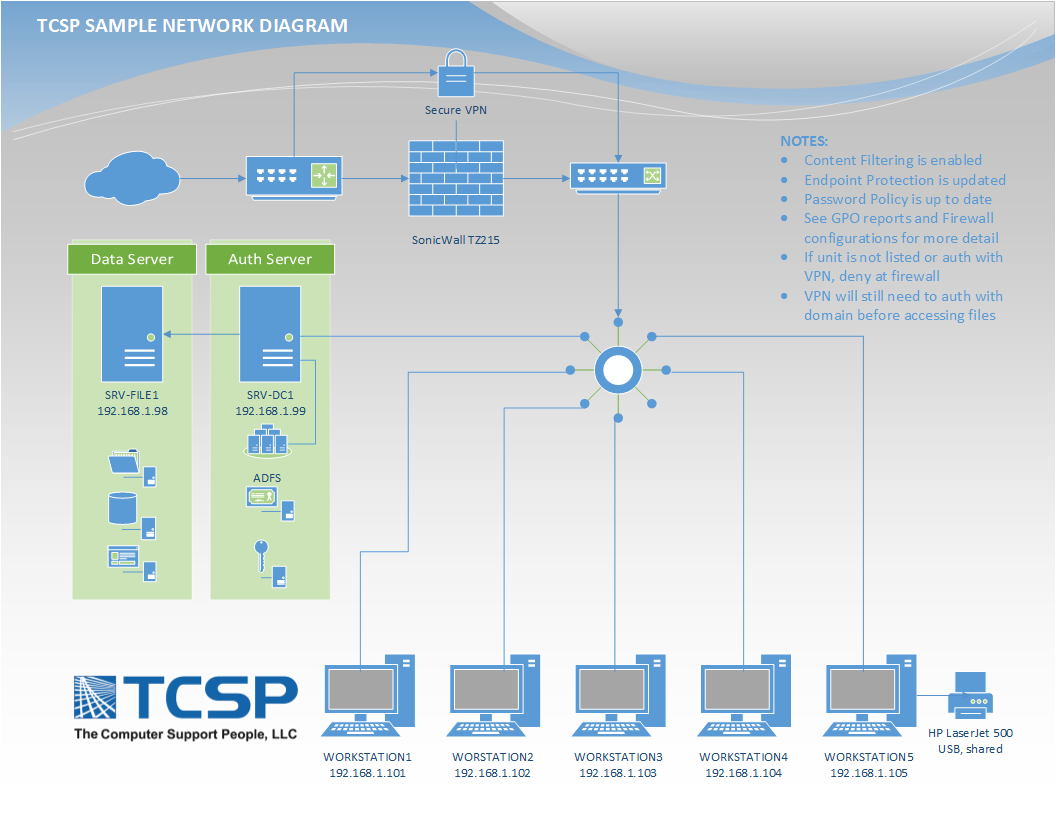
Proposed Security Design for LAN Topology 4.1 Active Directory Active... | Download Scientific Diagram

Figure 2 from Design and Implementation of a Network Security Model for Cooperative Network | Semantic Scholar